Sequence Groupings vs. Policy Blocks
Sequence Groupings
This will be a quick read on something I learned about this week: FortiGate Sequence Groupings. Originally I thought of this as a nested grouping of firewall rules on a FortiGate, but when prompted by a customer to figure out why we were unable to reorder Sequence Groupings I realized I needed to do some more research.
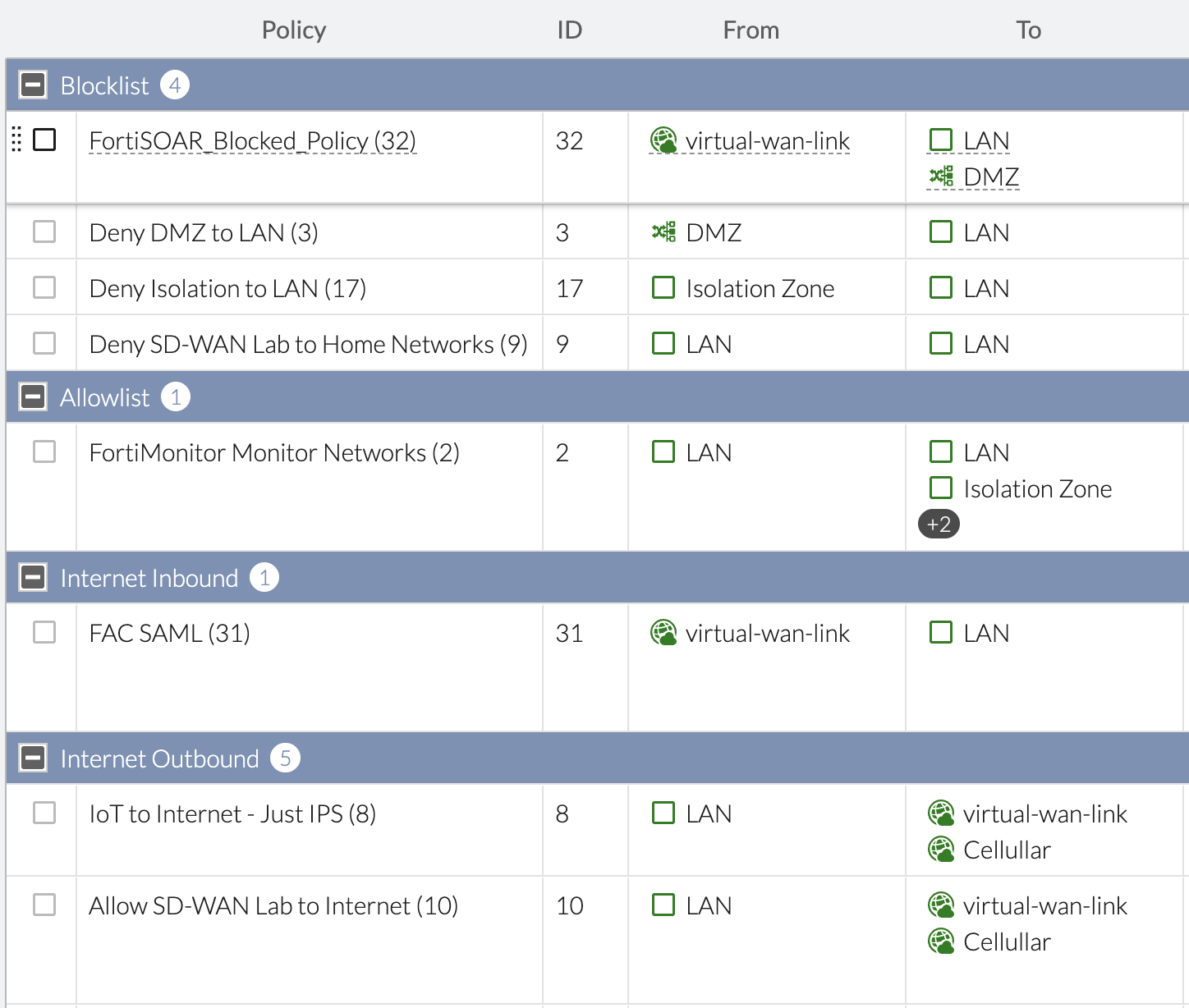
Example of Sequence Groupings
I had never used Sequence Groupings before today, but quickly appreciated the fact that it logically orders my firewall rules. When we view our rules by Sequence Grouping View In the screenshot above, we can see that I’ve created Sequence Groupings for my Blocklist, Allowlist, Inbound and Outbound sections and can collapse and expand each section to focus on the rules of interest in a long ruleset.
What exactly does creating a Sequence Grouping do in the FortiGate config? It' simply adds the set global-label "<sequence name>" config on the first rule in that Sequence. When does that Grouping end? When a further-down rule sets a different global-label.
In my screenshot above, that translates to this config:
config firewall policy
edit 32
set name "FortiSOAR_Blocked_Policy"
……
set global-label "Blocklist"
next
edit 3
…… (no global-label)
next
…… (no global-label)
edit 2
set name "FortiMonitor Monitor Networks"
……
set global-label "Allowlist"
next
…… (no global-label)
You might experience the “ahah” moment I had when I tried to reorder my Sequence Groupings to move one Grouping over another and was unable. It’s because it’s not a block, chunk or real group, it’s just a GUI-friendly label to organize your rules.
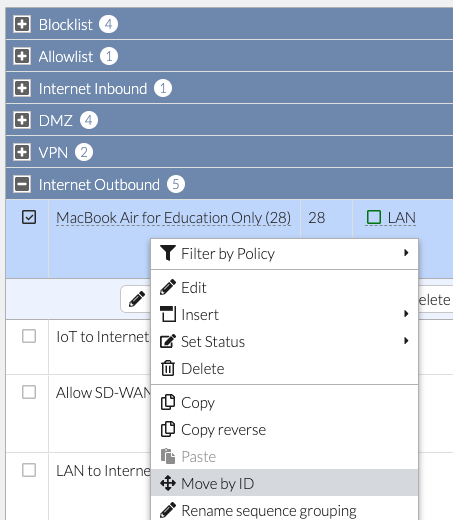
I can choose a rule and move it to another Sequence Grouping and that does reorder it, but I can’t move multiple rules at once by drag/drop or by trying to reorder the Sequence Groupings. So how do we work with that limitation? We will first move the rules to their desired destination one-by-one:
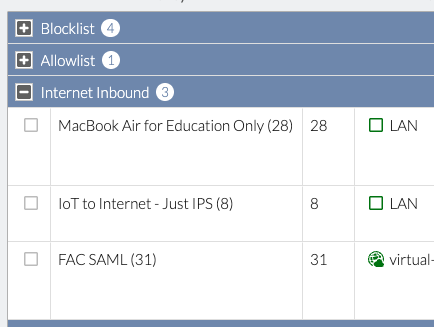
They’ll have the wrong Sequence Grouping at first (the MacBook Air and IoT rules aren’t Internet Inbound):
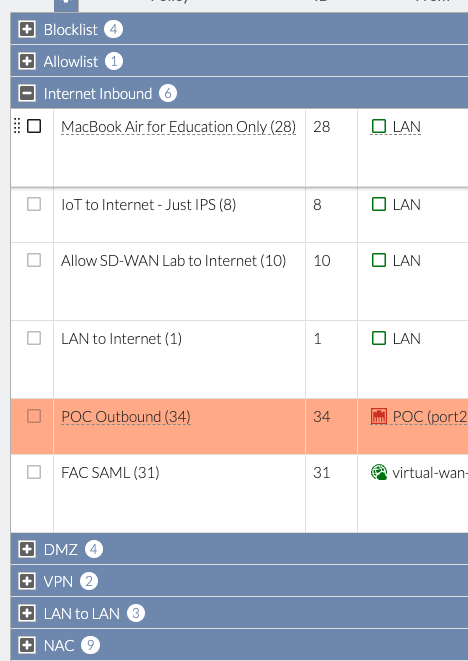
Repeat for all the rules and that will delete the old Sequence Group (no more Internet Outbound):
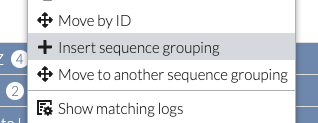
Since our “Internet Outbound” Sequence Group was deleted when we moved the last rule, we’re ready to recreate it in the appropriate section. Select the first rule in the wrong section (i.e. MacBook Air…) and “Insert sequence grouping” to create the “Internet Outbound” section:
Lastly, if any rules are still out of order we’ll right-click each rule and “Move to another sequence grouping” to clean them up.
The short story is these Sequence Grouping labels help you logically group the rules in the GUI but don’t combine the rules into something you can work with. You might ask yourself: isn’t there an easier way? There is!
Policy Blocks
If you use FortiManager, you’ve probably seen Policy Blocks before. If not, it’s hidden under Feature Visibility:
Policy Blocks are an easy way to reuse firewall rules across multiple Policy Packages. A Policy Block can be as simple as a header Blocklist or Allowlist at the beginning of each Policy Package. Or it can be as refined as a grouping of rules that are referenced further down the Policy Package (i.e. permit this group of employees to ChatGPT). The key thing to note is that what we were trying to achieve with Sequence Groupings by combining rules so we could easily reorder them — Policy Blocks in FortiManager does that.
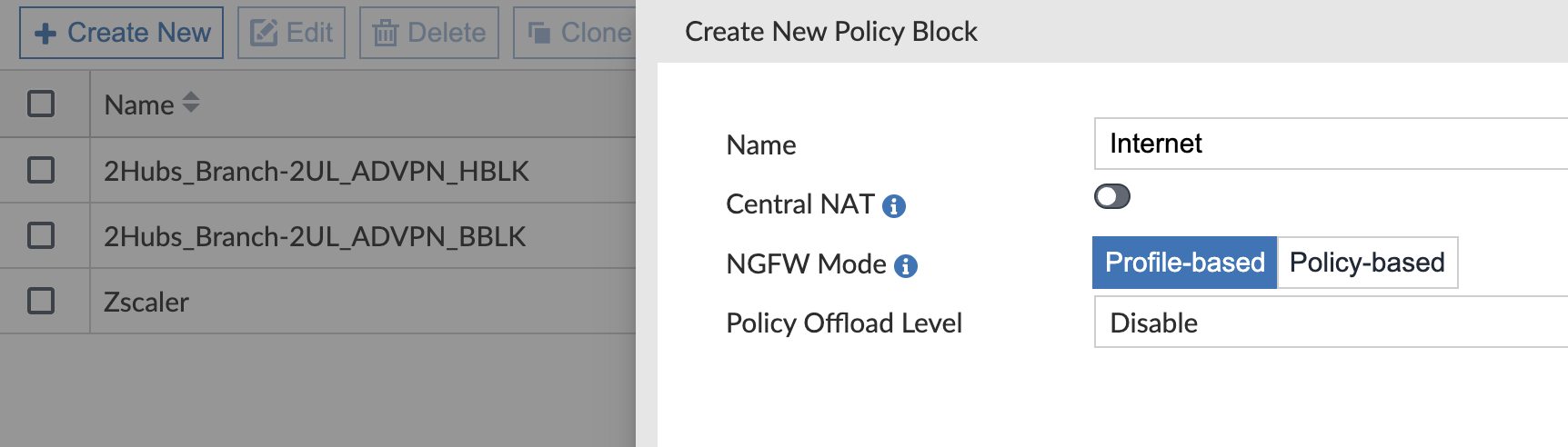
In FortiManager > Policy & Objects > Policy Packages > Policy Blocks, we’ll create a new one for Internet Outbound:
And we’ll add our firewall rules, just as we normally do:
In the above Internet outbound Policy Block, we give Manager’s unrestricted Internet access so they can do the hard work and make the big decisions for the company. They can’t be bothered by web-filters hindering their productivity to motivate us and drive our profits. And then everyone else will match the “DIA_OUT” rule with the web-filter for Corporate-approved websites.
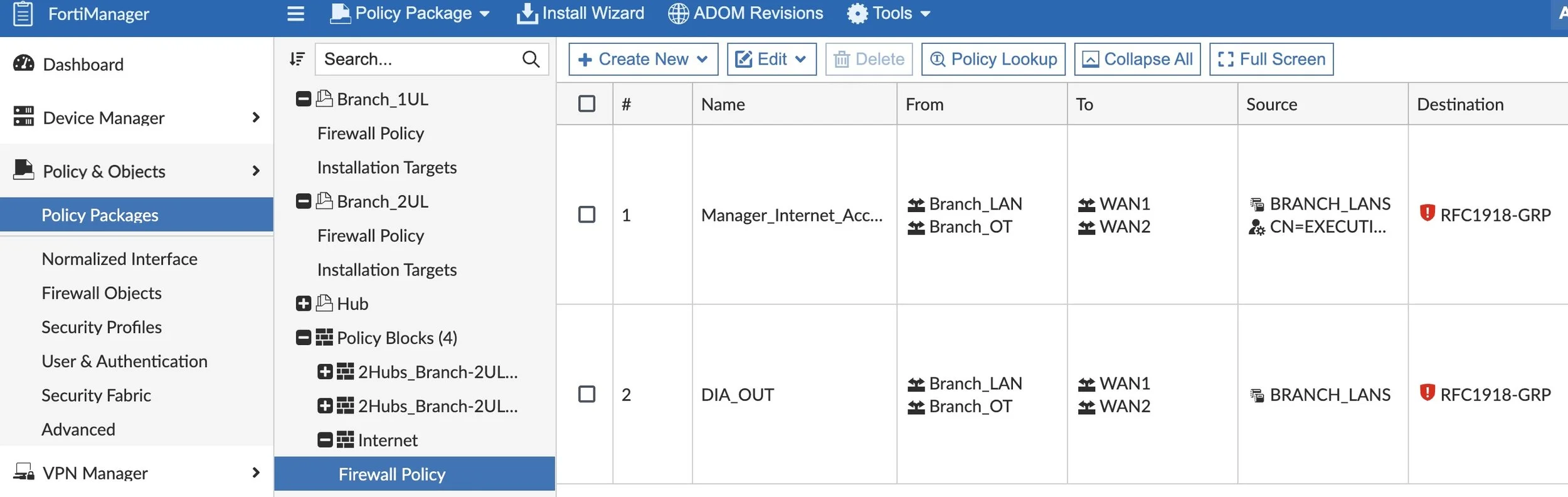
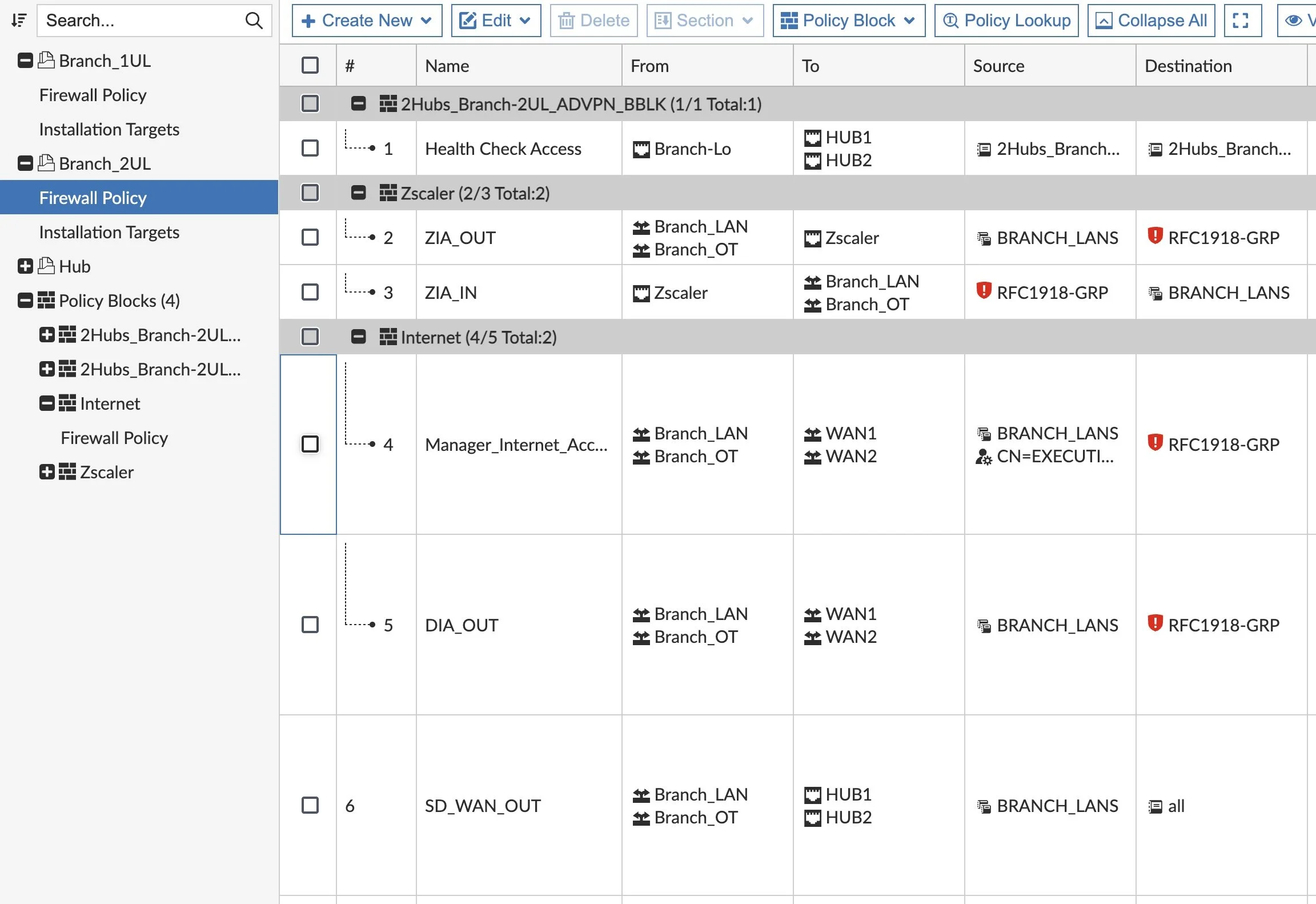
Now we go to our “Branch” Policy Package and insert the Policy Block where we’d like (such as above our “SD_WAN_OUT” rule):
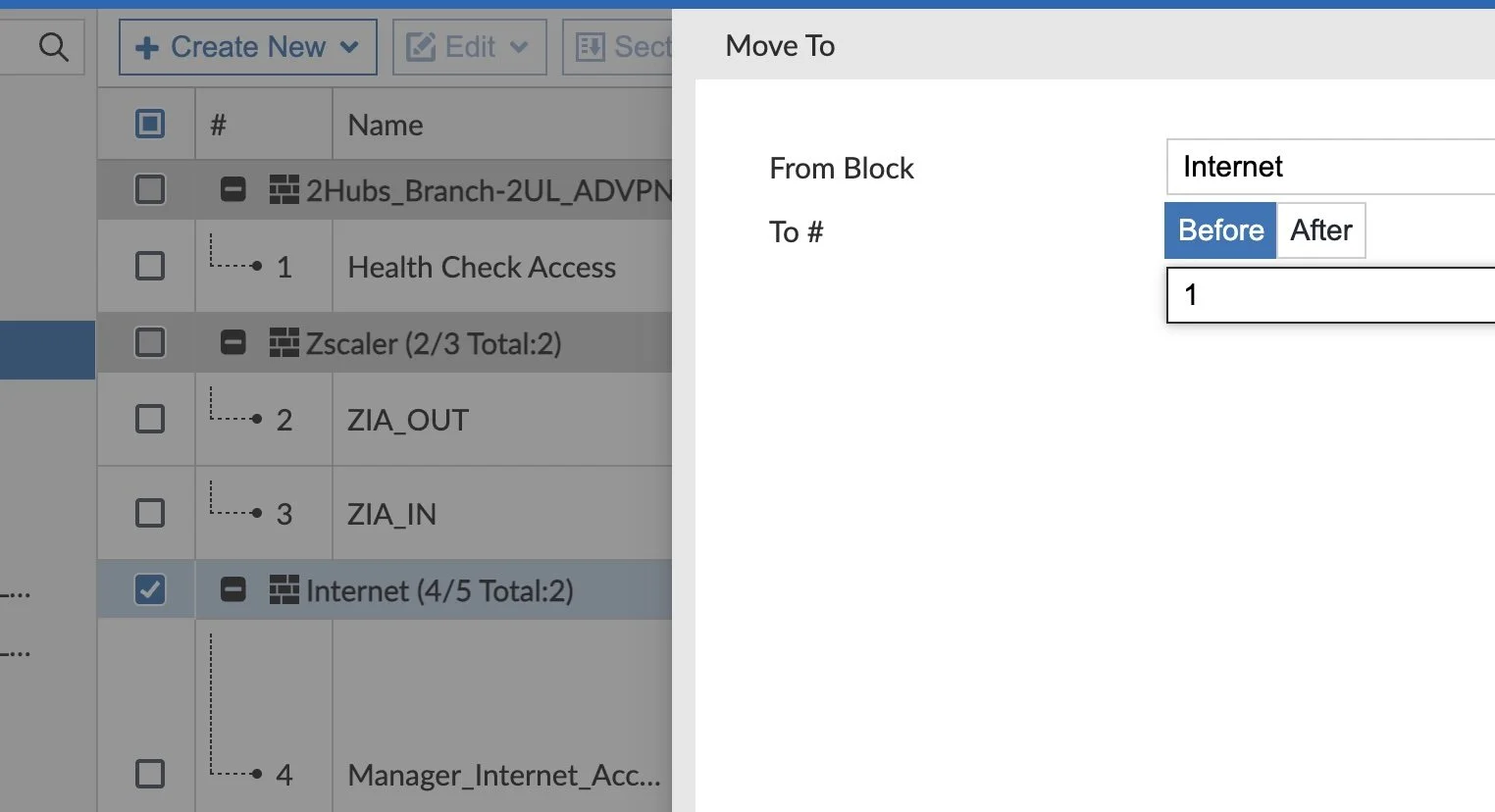
And if we’d like to reorder our Policy Blocks to place Internet at the top, we simply need to select our Policy Block, select the Policy Block menu and click Move Policy Block To for this window to pop up:
We’ll specify the ID of the rule we’d like to move this Policy Block before or after and that’s all there is to it.
Conclusion
I hope this short post helps explain how to achieve the goal to move groups of firewall rules (via FortiManager Policy Blocks) vs. labeling groups of rules (via Sequence Groupings on FortiGate or FortiManager). And you can still do both because both offer value in grouping and labeling our firewall rules.
Please comment below if you have use-cases for either solution. And thanks for reading!
Andrew